
WHITE PAPERS
Cybersecurity Challenges for Drinking Water Supply in Norway
Digitalization and increased automation have made water treatment and distribution systems more efficient, but also more vulnerable. As IT and OT converge, new risks emerge: from production shutdowns and contamination hazards to regulatory sanctions and loss of public trust.
As part of critical societal infrastructure, the drinking water supply is subject to specific requirements through the introduction of the new Digital Security Act, which will enter into force on 1 October 2025. This means that cybersecurity can no longer be viewed as an add-on — it must be an integrated part of operations.
This document provides insight into the threat landscape and demonstrates how SNOK® can contribute to more robust, secure, and stable operations of water treatment facilities in Norwegian municipalities and inter-municipal companies (IKS).
Lack of cybersecurity can have serious consequences
In the water sector, even minor incidents can have major consequences — for health, safety, and public trust:
- Supply interruptions: A short disruption in water production can quickly affect tens of thousands of residents and critical public services such as hospitals, schools, and fire departments.
- Contamination: Unauthorized access to control systems can lead to incorrect chemical dosing or manipulation of treatment processes, posing a serious health risk.
- Reputational damage: Trust in the water supply is essential. An incident that compromises water quality can have long-lasting consequences for both municipalities and residents.
- Regulatory consequences: The new Digital Security Act imposes reporting obligations, risk management, and incident handling requirements on water utilities. Failure to comply may result in sanctions and corrective orders.

Why is the water sector targeted?
- Lack of built-in security: Many control systems used in water utilities were not designed to support modern security mechanisms such as updates, antivirus software, or encryption without disrupting operations.
- Limited visibility and monitoring: PLCs, SCADA systems, pumps, and sensors are often not included in traditional security systems, creating blind spots.
- Weak network segmentation: Without a clear separation between IT and OT, an attack can spread rapidly across systems.
- Lack of OT expertise in IT and security teams: Most organizations have experience with traditional IT security, but not the specialized knowledge and tools required to secure industrial OT environments.
- Geographical dispersion: Water treatment plants and pumping stations are often distributed and unmanned, making continuous monitoring and effective incident response challenging.
Example from Norwegian reality: the Bremanger sabotageIn April 2025, hackers took control of the control system of a dam at Risevatnet in Bremanger — infrastructure with many parallels to water treatment facilities. The valves remained open for nearly four hours, releasing up to 500 liters of water per second before the attack was discovered and stopped (NRK, 13 August 2025).
Legally mandated security system
Cybersecurity in the water sector is no longer optional — it is a legal requirement. As part of critical societal infrastructure, water utilities are now covered by the Digital Security Act, which enters into force on 1 October 2025. The law is based on the EU’s NIS1 Directive and establishes clear frameworks for how water treatment facilities and distribution systems must be protected.
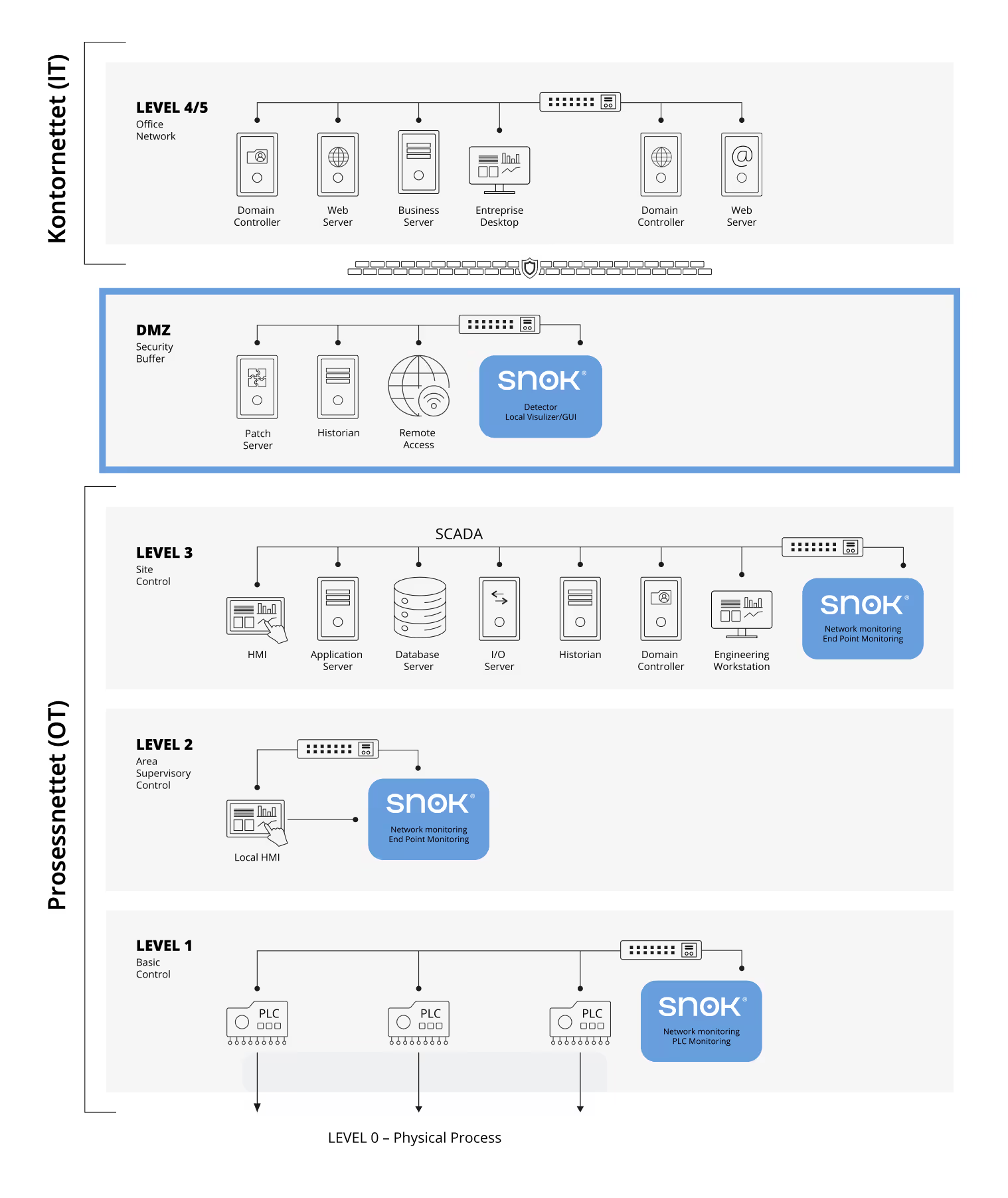

Our 3 Steps to Safer OT Operations — the most flexible cybersecurity platform for early detection of intrusions into operational systems.








