REQUEST A DEMO
Our 3 Steps to Safer OT Operations
Book a Demo
Three ways to start securing your OT environment

Physical Workshop
On-site session to establish a shared understanding of the OT environment, key risks and priorities, and align on expectations and scope.

OT Security Health Check
Time-limited assessment providing factual insight into OT assets, communication patterns and potential weaknesses, resulting in a documented security status.

Implementation &Continuous Operation
Implementation of agreed measures and continuous monitoring to support secure operations, compliance and long-term risk management.
Understanding SNOK® — common questions
Operational Technology (OT) security is a specialized field focused on protecting industrial automation and control systems (IACS) from cyber threats. It covers technologies that control critical infrastructure such as power grids, water treatment systems, and production lines in manufacturing facilities.
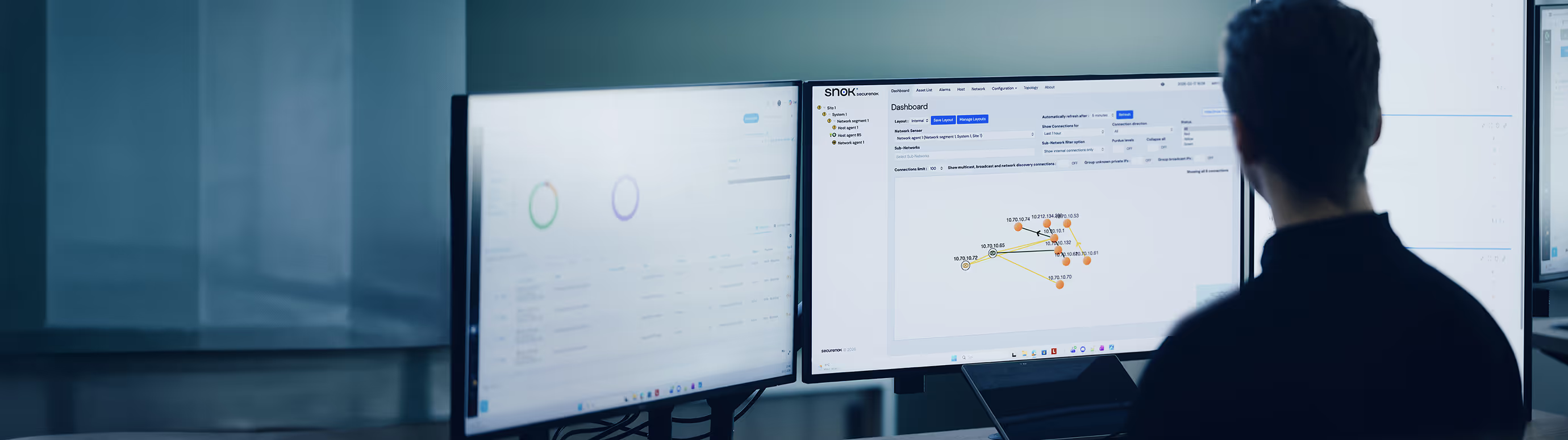
We offer the SNOK® platform, a cybersecurity monitoring system designed to detect early signs of intrusions. The solution consists of a unique combination of network sensors (NIDS), endpoint sensors, and PLC sensors, which together provide full visibility into the operational environment.
The risk has increased due to ongoing digitalization and the Industry 4.0 trend, which connects previously isolated production systems with IT networks. Cyberattacks have become a real threat to production continuity, employee safety, and the stability of public services.
IT security focuses primarily on protecting data, while OT security prioritizes the continuity of industrial processes and operational stability. OT systems often rely on legacy devices that do not support traditional security tools such as antivirus software or frequent updates to patch security holes.





